Description
Data Encryption & Key Management Services
-
End-to-End Data Encryption – Protects data across storage, transmission, and processing phases to prevent unauthorized access.
-
Centralized Key Management – Provides a unified platform to generate, distribute, rotate, and retire encryption keys securely.
-
Multi-Layer Encryption Support – Supports file-level, database-level, and full-disk encryption for comprehensive protection.
-
Hardware Security Module (HSM) Integration – Uses tamper-resistant hardware devices to securely store and manage cryptographic keys.
-
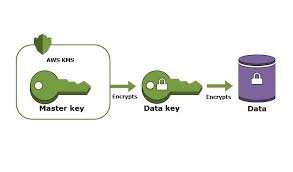
Cloud-Native Key Management – Integrates with cloud provider services like AWS KMS, Azure Key Vault, and Google Cloud KMS.
-
Access Control & Policy Enforcement – Ensures only authorized users and systems can access or manage encryption keys.
-
Automated Key Rotation – Periodically updates keys to maintain compliance and reduce the risk of key compromise.
-
Data-at-Rest Protection – Encrypts stored data on databases, disks, and backups to ensure confidentiality and compliance.
-
Data-in-Transit Encryption – Uses TLS/SSL and VPNs to protect data during transmission over public or private networks.
-
Role-Based Access Management (RBAC) – Restricts key access and operations based on user roles and organizational policies.
-
Audit Logging & Compliance Reporting – Tracks key usage and encryption activities for auditing and regulatory compliance.
-
Multi-Cloud & Hybrid Support – Manages encryption and keys consistently across multiple cloud providers and on-premises systems.
-
Integration with Security Tools – Works seamlessly with SIEM, DLP, and IAM systems for unified security management.
-
Regulatory Compliance Alignment – Helps meet standards such as GDPR, HIPAA, PCI DSS, and ISO 27001.
-
High Availability & Scalability – Ensures continuous key access and encryption services even in large-scale or distributed environments.

Reviews
There are no reviews yet.